The emerging Docker containers have potential to revolutionalize NFV.
After all, they are lightweight compared to virtual machines; they need less overhead and resources; and, they can provide application isolation running in the same operating system, they live in.
That means, if a Virtual Network function (VNF) in NFV can run in a Docker container with complete isolation, you may not need a virtual machine.
But, is it that easy?
And what is the future of virtual machine, then?
Infact, it is too early to say anything about the future of virtual machines as docker containers are still evolving ( and so is NFV ![]() ).
).
However, if you stay till the end, you will be able to find out, what makes Docker containers so special that everyone is talking about them now.
The primary aim of this guide is to walk you step by step in understanding the architecture of Docker container. In the process, you will also understand the basics of the hypervisor and virtual machine.
The concepts are explained, assuming zero prior knowledge about virtual machines and hypervisors.
What is a container?
Historically, containers emerged as a way of running applications in a more flexible and agile way. Linux containers enabled running lightweight applications, within Linux OS directly. Without a need for the hypervisor and virtual machines, applications can run in isolation in the same operating system.
What is a Docker container?
Google has been using Linux containers in its data centers since 2006. But, they became more popular with the arrival of docker containers in 2013. Which is a more simple and standard way to run containers compared to earlier version of containers.
The Docker container also runs in Linux. But Docker is not the only way run containers. LXC is another way to run containers. Both LXC and Docker have roots in Linux.
One of the reasons, the Docker container is more popular compared to competing containers such as LXC is its ability to load as “image” on host operating system in a simple and quick manner. Dockers are stored in the cloud as images and called upon for execution by users when needed in a simple way.
Moving forward, I will use the word “container” and “Docker container” interchangeably as the concepts apply to both.
Step by Step guide to understanding Docker containers in NFV
Virtual machines are good, yet they have problems:
You need a dedicated operating system. And, you need a hypervisor to separate the virtual machine to achieve virtualization.
More applications mean more software overhead, more expensive and a need to keep them updated.
Yet, virtual machines are needed for NFV architecture, so let’s see the NFV architecture.
Step 1: Let’s start with the Hypervisor in NFV Architecture
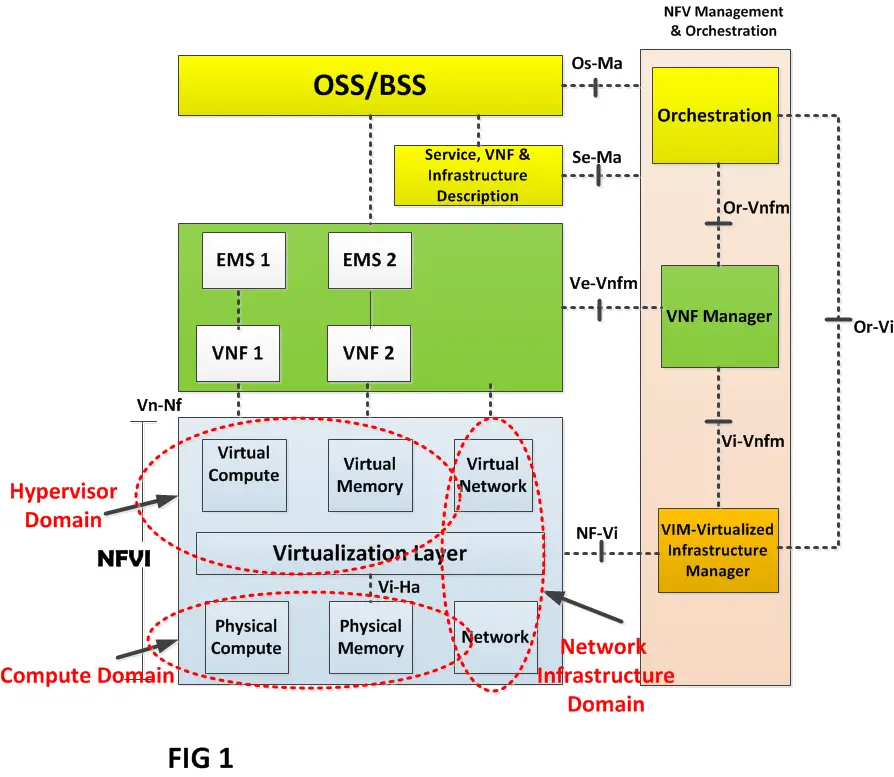
In this diagram, I am showing the NFV architecture, you may have seen many times ( Need a refresher, visit here).
For the purpose of this discussion, I will zoom only on the NFVI ( NFV Infrastructure) that has three distinct components:
The Hypervisor domain, the Compute domain, and the Network Infrastructure domain.
The virtualization layer is actually the hypervisor, which is responsible for abstracting the hardware resources of a compute domain (physical/x86 servers). For example, you may have a single physical server ( physical memory and physical compute) but the hypervisor can partition it into multiple virtual memories and virtual computes in a way that each entity is independent.
Together, the virtualization layer ( which we called hypervisor) with the virtual resources is called “Hypervisor domain”.
Step 2: Lets zoom in Virtual Machines
To understand virtual machines, I will now expand the hypervisor domain to show what is inside this domain.
Have a look at Fig 2 below:
I am showing on the left the same Hypervisor domain as in Fig1 above. But in the figure to the right, I have expanded the Hypervisor domain to show the virtual machines. That is, the virtual resources of the hypervisor domain are now shown as virtual machines.
For simplicity, I have removed the virtual network/network blocks on the left, as they are not important for this discussion.
The virtualization layer has become the resource/network manager. The virtual compute/memory has become virtual machine (VM)
So what is a virtual machine?
A virtual machine provides an environment in which a VNF ( Virtual Network Function) runs.
If you look at the diagram, each Virtual Machine is linked to a VNF .
Let’s take an example to clarify. There is a VNF1 called Virtual CPE and another VNF2 called Virtual Firewall. From the example above, each then runs into its own virtual machine. They can then be chained and connected internally through a hypervisor domain.
Also, note that virtual machines are logically separate from one another. This makes it possible to run independent operating systems on each virtual machine. For example, Guest Operating System OS1 can be Linux and Guest OS2 can be Solaris (as an example).
And in addition to the Guest operating systems/OS, did you notice that there is also a need for Host Operating System/OS, which is an environment in which the hypervisor runs.Keep this important point in mind, as I discuss containers in the next paragraph.
Let’s take the journey forward and now remove the Virtual Machines.
Step 3. Remove virtual machines and introduce containers!
Now instead of virtual machine, I introduce a totally new component Container
VNF1 now runs in container 1 and VNF2 runs in container 2 providing the same functionality as virtual machines.
What we have achieved is the same functionality as a virtual machine but within the same OS, which is Linux here.
Did you notice that there is no need for Guest OS now?
Simple architecture; isn’t it?
What have we achieved with containers?
1. There is no need for Guest Operating System (OS) in the container environment as you can see that the Host OS is Linux. Therefore, they are lighter weight and need less overhead compared to virtual machines
2. Architecture is simplified by removing the hypervisor as now the containers can retain sufficient isolation at the OS level inside the same Host OS.
3. Virtual Machine provides hardware level virtualization meaning classic virtual machines take a host and partition it via hypervisor software. This essentially means that VMs are isolated from the OS of the host machine. You can run a windows Host over a Linux operating system.On the other hand, containers provide OS level virtualization. That is in the same OS, applications can keep themselves isolated. This is far less overhead compared to VM as the whole OS is not duplicated.
That’s it about the Containers.
Future of containers for NFV
Let’s face it, the current NFV architecture and standards are based on the Virtual machines.
Containers are still new to NFV. There are still a lot of development going on especially from a security point of view. As you can see that the Host OS is exposed to all containers so there could be potential multi-tenancy security issues.
However, they do promise a good future considering the ease and simplicity of running the VNFs in such environments. Also, they can open a door to running microservices instead of running a complete VNF over a virtual machine.
For example in the case of virtual CPE, a lot of its components can be decomposed into small containers and chained together. By decomposing the functions, this will provide an opportunity for small software vendors to develop small functions of a VNF easily with less overhead.
Did this guide help you in understanding the containers in a simple way ?
Share your views in the following comments section.

![clip_image003[4] clip_image003[4]](https://telcocloudbridge.com/wp-content/uploads/2016/03/clip_image0034_thumb.png)
![clip_image004[4] Docker container in NFV](https://telcocloudbridge.com/wp-content/uploads/2016/03/clip_image0044_thumb.png)
Hi Fasal,
As usual, your write is useful and accurate and you give a good sharing.
Talking about the container, maybe it is worth to mention few points more:
1- today the security of Linux container has been increased and the level of needed isolation is pretty good. But it is not enough.
2- I do think that operational agility is the real enabler for a right SDN/NFV deployment, so without a doubt I agree NFVI needs to handle container technology too. But not only. The demand of following a service model design means the need of complex service chain, based on atomic components deployed with different computing (and Network) QoS. So the NFVI must be able to handle both VMs and containers concurrently and that is where the issue comes. We need a unique controller for them and we need a message passing mechanism valid for both (and efficient enough).
3- Containers benchmarks show they are efficient for fast migration and fast creation, but the cost of the virtualization is not so better than VMs one. Using container for PoP services could be done, of course, but surely performance improvement is not the reason behind.
Hello Carlo,
Thank you
You brought up very valid points. I agree that NFVI should be able to handle both containers and VMs. One of the issue I feel is the dynamic and rapid changing scenes of new technologies which makes it difficult to roll out standards quickly like the one you mentioned. For example the whole focus of ETSI is on VMs and containers are for future studies. Coming back to your point, Yes if there would be containers and VMs running in parallel, there would a need for a unique controller to handle the task of managing them, which will make the situation quite complex.
I think this is available in OpenStack, it can manage both VM and container.
Thanks for sharing
Thanks for sharing, it’s really nice to see your posts Faisal
Thanks Javed, for taking time to read the article.
Thanks alot sharing this docs. I really like the way you explained the things and with beautiful self explanatory diagrams.
Really excellent Job.
Keep on sharing the docs , looking forward for more docs in virtualization and openstack domain.
Thanks Pawan! that you liked it.
Hi Faisal, excellent overview. Thank you
Thanks Moshref, for reading and commenting !
Good work Faisal. Keep your views coming they are good. Cheers.
Thank Randy! that you liked the blog !
Another good article Faisal. You should write more often. 🙂
Thanks Manik Sidana ! for your encouraging comments !
Hi Faisal
In Hypervisors there is the vSwitch which allow network connection between VM.
What is the equivalent of vSwitch in Dockers?
Thanks
Dudu
Hello Dudu,
Thanks,
Have a look at Socketplane that brings SDN functionality for networking in Dockers.
http://socketplane.io/
Congrats, Faisal! A must-read for those who are following the milestones of NFV.
Thanks Claudio! that you liked the post
The explanation and the architectural diagrams that you used are great! Thank you
Faisal…excellent & informative article. Please keep posting.
Thank you Rajesh!that it helped you
Very nice introduction. Love your plain and lucid writing style.
Look forward to reading more advanced posts from you on containers,
especially container networking, kubernetes, etc.
Thanks Farhad for stopping again to read the blog….
I will take a note of the topics !
Faisal, excellent as usual. Your posts have become part of my favourite tech readings. Roland
Thanks Roland ! For regularly visiting the blog and liking it !
As a graduate student learning SDN/virtualization topics, we had this discussion about VMs and containers in last week’s lecture. I didn’t quite understand the difference until I saw your post. With your style of explanation, it is very easy to understand the topic. Thanks for sharing it, Faisal.
Hello Sanket,
Glad that the post was of help. Keep visiting back !
As usual, very good explanation. Waiting for more in depth writing about docker in NFV.
Hope to get your next master piece soon. 🙂
Hello Faisal
Awesome article on containers and NFV. It’s detailed and lot simpler understanding the concept.
Have you set up either SDN or NFV in a lab environment, if yes could you direct me, I have tried installing devstack but miserably failed several times
Thanks Sanjeeve for visiting and commenting.
Sorry, I did not setup SDN/NFV in a lab environment.
I have installed a sample NFV using Tacker
DevStack is a development version of OpenStack. If you want to develop, share, and experiment with OpenFlow and Software-Defined Networking systems, try Mininet
http://mininet.org/
Thank you Faisal for the nice article and for keeping it very simple. Was looking to read about Docker containers concept and came across this blog which made it easy for me.
Quick Q..
If I have a VNF built to be deployed on Windows and if my Docker is on Linux, do I need to port my VNF to run on Linux? By using containers are we loosing the OS abstraction we get to gain by using VM?
Regards
Srinivas
You are correct Srinivasa !
And thank you for visiting and commenting.
Good view 🙂
Thanks Ivay for visiting and commenting
Nice article. Simple, clear and easy to understand writing!
Thanks for sharing.
Thanks Gandhimathi!
My comments come a little bit late, but here’s my question:
How to choose the shared OS (kernel)? As far as I know, most VNFs have certain degree of dependency on Linux kernel, hence migrating VNF to container means decouple application and kernel completely, and that’s a lot of work to do.
Do you by any chance know any successful implementation of VNF in container?
Thanks for the great article by the way.
Thanks Daniel, I know a lot of work is going on with containers in NFV. For example on link as below for your reference
blog.imaginea.com/experimenting-with-containers-in-the-nfv-world/
Thank you for making the Docker container more enlighten to me. NFV/SDM is quite trending and the future of virtualization and IT lies on its shoulder.
thanks again
Thanks Jesse for stopping over!
Hi,Faisal Khan
I’m a master’s student from Taiwan.
I can realize Container technology is more simple then Virtual Machine.
But when I run many VNF(container) on a single physical host, they shared same resource from physical host. So we can’t effectively allocate resource to VNF, Isn’t it?
If my telecom architecture have a service chain and I user Container technology to implement it. There is one node will be the bottleneck in this service chain. This node will use almost all resource of the physical host.
I want to auto scale out the VNF node which cause bottleneck in service chain. But I think there is no necessary to scale out because it will use almost resource of the physical host. So I have no resource to scale out new VNF. Is that right?
THANKS eggcheng,
you can run multiple containers on single host.
Assalamo Alaikum Faisal,
Very nice article. Good explanation of containers vs VMs and in very simple manner.
Thank you Omair , Keep on visiting
pretty good article. Like it.
One problem with Container is (compare to VM) is Security. As they share Kernel (for system calls) so complete isolation claim is perhaps not true.
Thanks Azhar. I agree with you. Security for containers is one of the hot topics these days.
Hi,
What’s the difference between Container and a process? Within a single OS (say Linux) different process have total isolation?
What’s the need to have a Container do the same thing.
Please clarify.
Sincerely
Sudarsan.D
You wrote it very well. I really liked it.
But respectfully, I disagree with following lines of your article;
“Did you notice that there is no need for Guest OS now?
1. There is no need for Guest Operating System (OS) in the container environment as you can see that the Host OS is Linux. Therefore, they are lighter weight and need less overhead compared to virtual machines”.
I have created containers of centos and opensuse which run on ubuntu (host O/S). Though these are all linux flavors but they are different operating systems. However, they do share common Kernel which is the beauty of Containers.
So perhaps it is more appropriate to say that “there is no need for Guest O/S Kernel in the container environment.” The resources are assigned dynamically, therefore sometimes my centos grabs more compute resources than opensuse and vice versa depending on need basis.
Thanks Azhar,
Thank you so much for your comments. You are correct. Actually, the article was looking at a more conceptual level.
Thank you very much for the article. I have just dipped into the NFV world and still figuring a lot of things out. But your article is an excellent step down to noobs like me. I will keep on reading articles from you and explore how can I appreciate other articles in the world. Heartfelt thanks to you and thank you for sharing. Aspire to be someone like you in future.
Thanks Jonney,
Glad that you liked it. More is coming soon
Wow. That is so elegant and logical and clearly explained. Keep it up! I follow up your blog for future post.
Glad that you liked it !
Containers are good for start,but what if there is an kernel panic in host os which has an high probability in case of telco deployments and since the kernel and network resources are shared there will be an potential outage.Is there any work going on to overcome this issue.
Perhaps need more info on that. PM me.
Excellently articulated article! Would you consider updating this 2016’s blog in 2020 to accommodate the recent developments in the container world?
Thanks for the feedback Rajesh !
Thanks Rajesh, Noted
Thanks Faizal for your wonderful articles !
Do you have any article written over kubernetes platform hosted over the openstack VMs. Kindly share in terms of telco workloads
Thanks Suchetan Singh for visiting and commenting. Unfortunately I do not have one